Note_Tech
All technological notes.
Project maintained by simonangel-fong Hosted on GitHub Pages — Theme by mattgraham
AWS - Certificate Manager (ACM)
AWS Certificate Manager (ACM)
-
Usage
- Easily provision, manage, and deploy
TLS Certificates - Provide
in-flight encryptionfor websites (HTTPS)
- Easily provision, manage, and deploy
-
features
- Supports both public and private TLS certificates
- Free of charge for public TLS certificates
- Automatic TLS certificate renewal
-
Integrations with (load TLS certificates on)
Elastic Load Balancers(CLB, ALB, NLB)CloudFrontDistributions- APIs on
API Gateway
-
Cannot use
ACMwith EC2 (can’t be extracted)
Requesting Public Certificates
- List domain names to be included in the certificate
Fully Qualified Domain Name (FQDN):- e.g.:
corp.example.com
- e.g.:
Wildcard Domain:- e.g.:
*.example.com
- e.g.:
- Select Validation Method:
DNS ValidationorEmail validationDNS Validationis preferred for automation purposes- will leverage a
CNAMErecord toDNS config(ex: Route 53)
- will leverage a
Email validationwill send emails to contact addresses in the WHOIS database
- It will take a few hours to get verified
- The
Public Certificatewill be enrolled for automatic renewal- ACM automatically renews ACM-generated certificates 60 days before expiry
Importing Public Certificates
- Option to generate the certificate outside of ACM and then import it
- No automatic renewal
- must import a new certificate before expiry
- ACM sends daily expiration events starting 45 days prior to expiration
- The # of days can be configured -
- Events are appearing in
EventBridge
AWS Confighas a managed rule namedcm-certificate-expiration-checkto check for expiring certificates (configurable number of days)
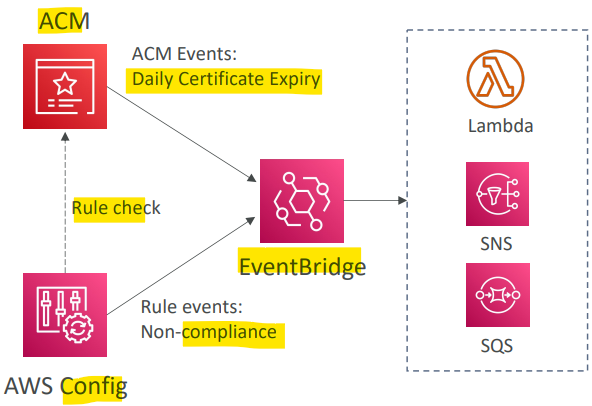
- Sample:
- You have generated a public certificate using LetsEncrypt and uploaded it to the ACM so you can use and attach to an Application Load Balancer that forwards traffic to EC2 instances. As this certificate is generated outside of AWS, it does not support the automatic renewal feature. How would you be notified 30 days before this certificate expires so you can manually generate a new one?
- Configure EventBridge for Daily Expiration Events from ACM to invoke SNS notifications to your email
- You have generated a public certificate using LetsEncrypt and uploaded it to the ACM so you can use and attach to an Application Load Balancer that forwards traffic to EC2 instances. As this certificate is generated outside of AWS, it does not support the automatic renewal feature. How would you be notified 30 days before this certificate expires so you can manually generate a new one?
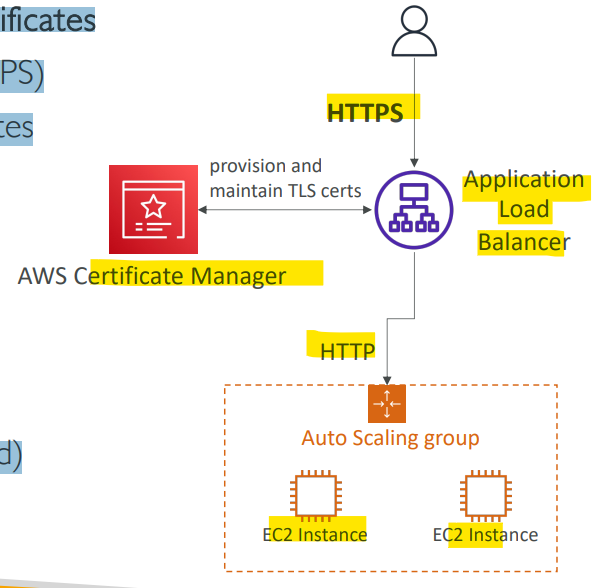
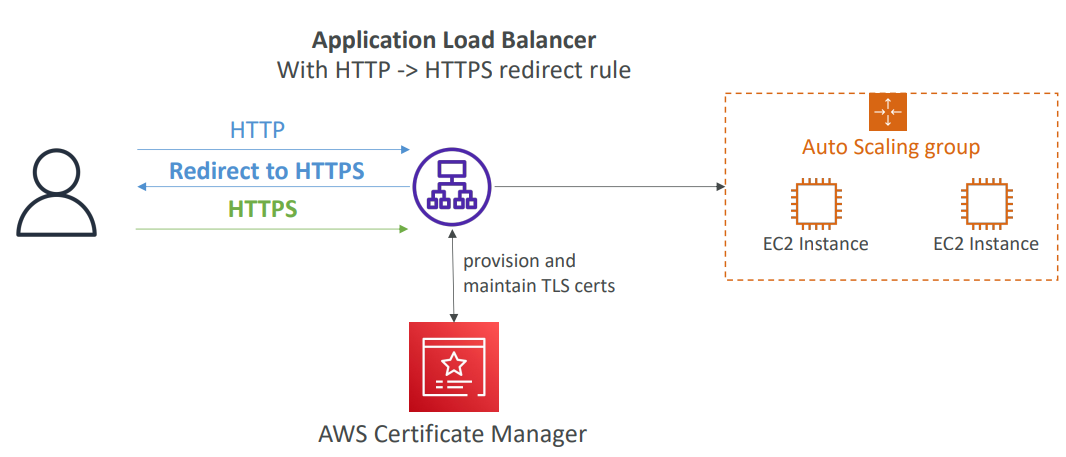
Example: Integration with ALB
- Set a redirect rule in ALB to redirect a
HTTPrequest to aHTTPSrequest.
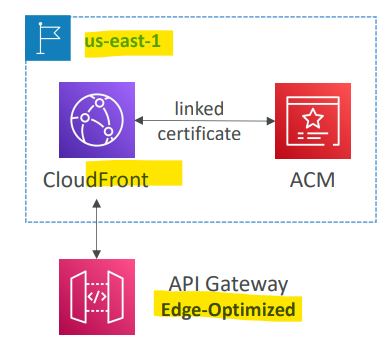
Example: Integrate with API Gateway
-
Based on different Endpoint Types
-
Create a
Custom Domain Namein API Gateway -
Edge-Optimized (default):
- For global clients
- quests are routed through the CloudFront Edge locations (improves latency)
- The API Gateway still lives in only one region
- The
TLS Certificatemust be in the same region asCloudFront, i.e.:us-east-1 - Then setup CNAME or (better) A-Alias record in Route 53
-
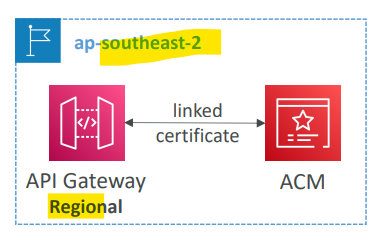
Regional:
- For clients within the same region
- The TLS Certificate must be imported on API Gateway, in the same region as the API Stage
- Then setup CNAME or (better) A-Alias record in Route 53
-
Private:
- Can only be accessed from your VPC using an interface VPC endpoint (ENI)
- Use a resource policy to define access
- Not mention.
-
Sample:
- You have created the main
Edge-Optimized API Gatewayin us-west-2 AWS region. This main Edge-Optimized API Gateway forwards traffic to the second level API Gateway in ap-southeast-1. You want to secure the main API Gateway by attaching an ACM certificate to it. Which AWS region are you going to create the ACM certificate in?- us-east-1
- As the
Edge-Optimized API Gatewayis using a custom AWS managed CloudFront distribution behind the scene to route requests across the globe through CloudFront Edge locations, the ACM certificate must be created inus-east-1.
- You have created the main