Note_Tech
All technological notes.
Project maintained by simonangel-fong Hosted on GitHub Pages — Theme by mattgraham
AWS - KMS
- AWS - KMS
AWS KMS (Key Management Service)
- Anytime you hear “encryption” for an AWS service, it’s most likely KMS
- AWS manages encryption keys for us
- Fully integrated with
IAMfor authorization - Easy way to control access to your data
- Able to audit
KMS Keyusage usingCloudTrail -
Seamlessly integrated into most AWS services (EBS, S3, RDS, SSM…)
- Never ever store your secrets in plaintext, especially in your code! (可以储存密钥, 但不能是明文)
KMS Key Encryptionalso available through API calls (SDK,CLI)- Encrypted secrets can be stored in the code / environment variables
Keys Types
-
KMS Keys- the new name of
KMS Customer Master Key
- the new name of
-
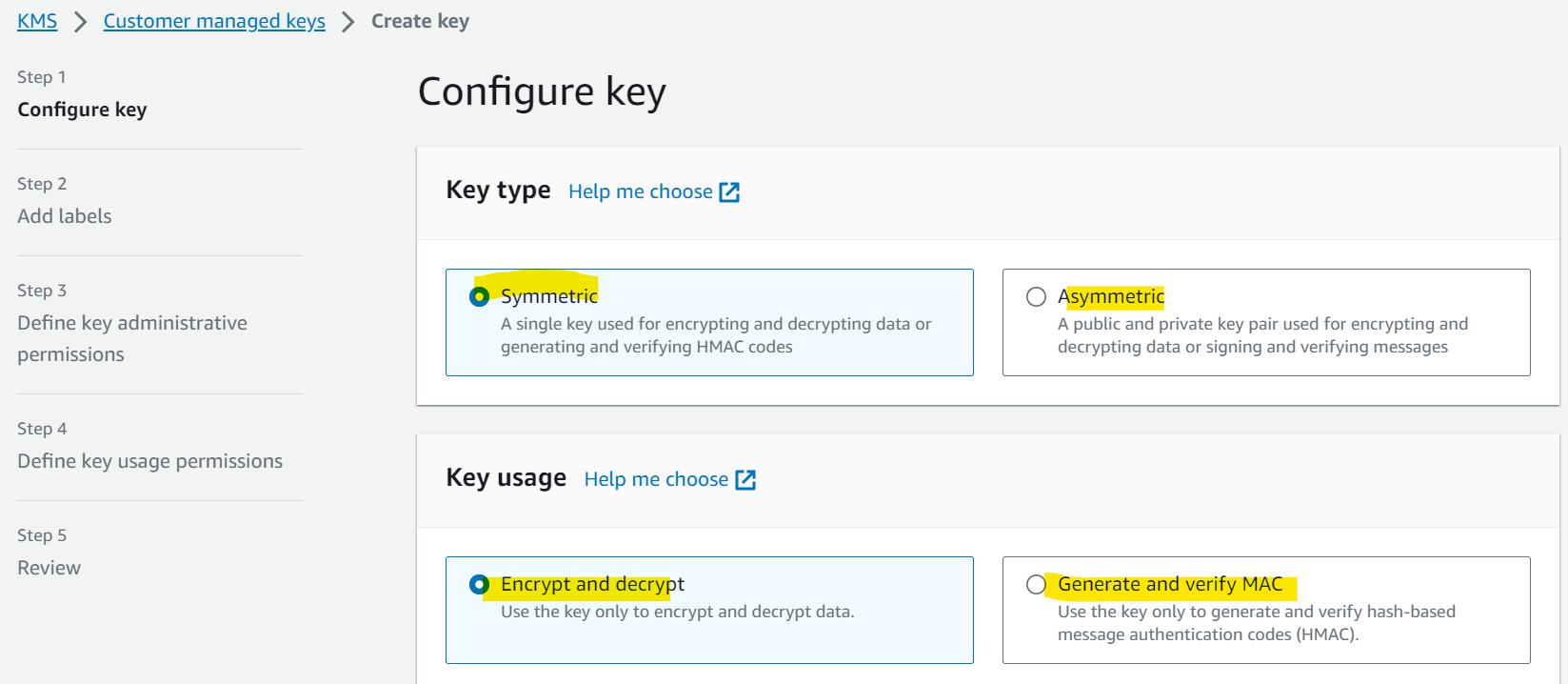
Symmetric (AES-256 keys)
- Single encryption key that is used to Encrypt and Decrypt
- AWS services that are integrated with KMS use
Symmetric CMKs(Customer Master Key) - You never get access to the KMS Key unencrypted
- must call
KMS APIto use
- must call
-
Asymmetric (RSA & ECC key pairs)
- Public (Encrypt) and Private Key (Decrypt) pair
- Used for
Encrypt/Decrypt, orSign/Verifyoperations - The public key is downloadable, but you can’t access the
Private Keyunencrypted - Use case:
- encryption outside of AWS by users who can’t call the KMS API(外人用 public key 加密, 自己用 private key 解密)
-
Types of KMS Keys:
- AWS Owned Keys (free):
- e.g.:
SSE-S3,SSE-SQS,SSE-DDB(default key)
- e.g.:
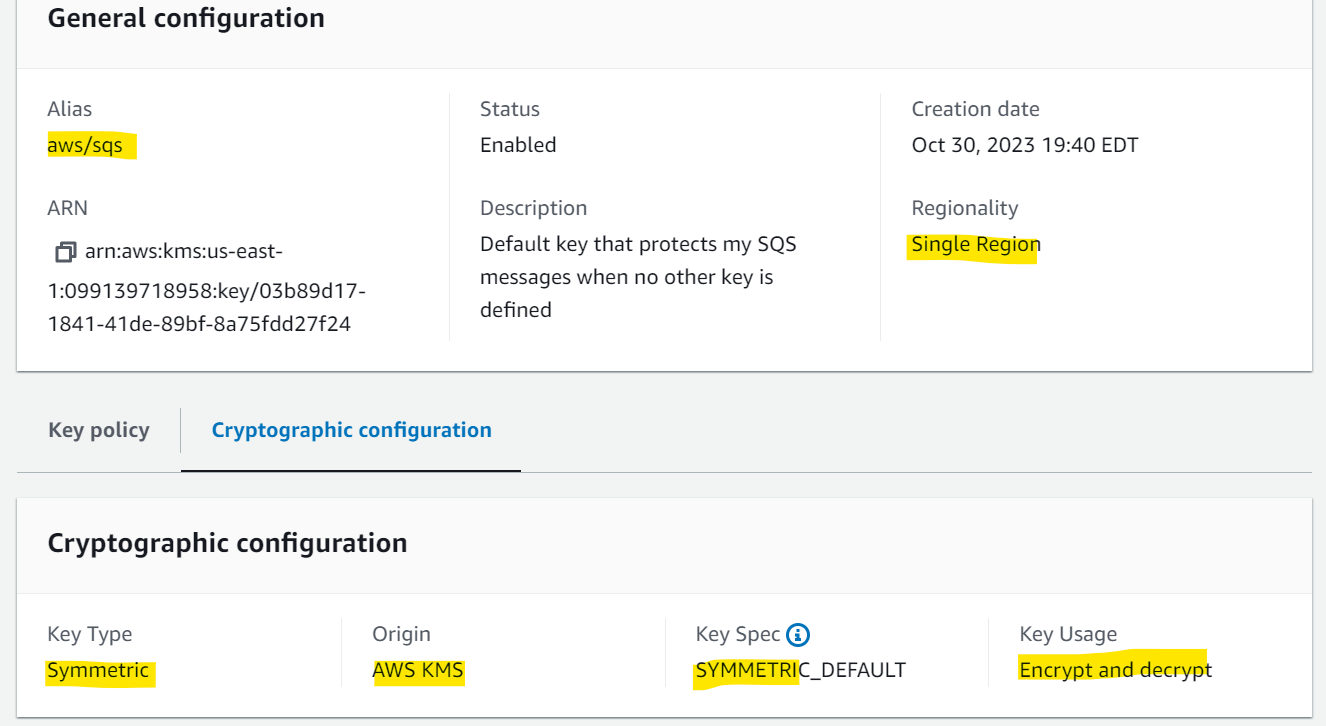
- AWS Managed Key: free
aws/service-name- e.g.:
aws/rdsoraws/ebs
- Customer managed keys created in KMS:
- $1 / month
- Customer managed keys imported (must be symmetric key):
- $1 / month
- AWS Owned Keys (free):
-
pay for
API callto KMS ($0.03 / 10000 calls) -
Sample:
- You need to create
KMS Keysin AWS KMS before you are able to use the encryption features for EBS, S3, RDS …- false
- You can use the
AWS Managed Servicekeys in KMS, therefore we don’t need to create our own KMS keys. - only customer keys need creation beforehand
- AWS KMS supports both symmetric and asymmetric KMS keys.
- true
- You need to create
Key Rotation
-
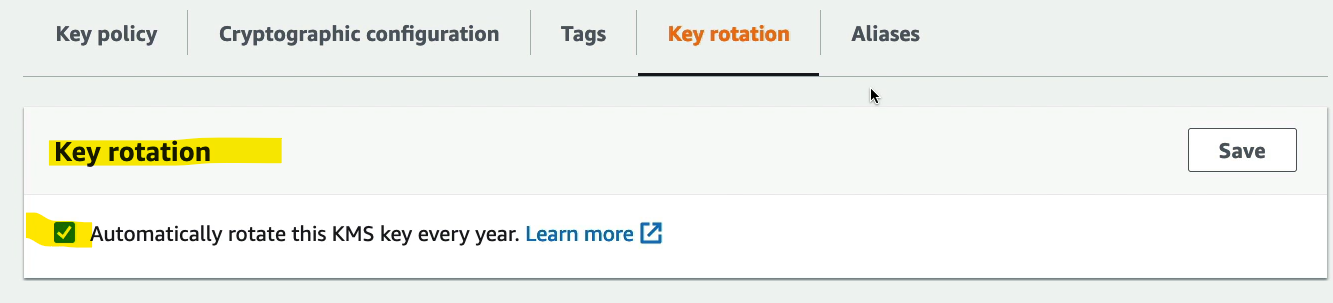
Automatic Key rotation:
- AWS-managed KMS Key:
- automatic every 1 year
- Customer-managed KMS Key:
- (must be enabled) automatic every 1 year
- Imported KMS Key:
- only manual rotation possible using alias
- AWS-managed KMS Key:
-
Sample:
- When you enable Automatic Rotation on your KMS Key, the backing key is rotated every ……………..
- 1 year
- You have created a Customer-managed CMK in KMS that you use to encrypt both S3 buckets and EBS snapshots. Your company policy mandates that your encryption keys be rotated every 3 months. What should you do?
- Rotate CMK manually. Create new CMK and use aliases to reference the new CMK. Keep old CMK to decrypt.
- When you enable Automatic Rotation on your KMS Key, the backing key is rotated every ……………..
-
技术方法
- 对称, 单一钥
- 非对称, 公钥密钥
-
所有权
| Types | Description | Rotation |
|---|---|---|
| AWS Owned Keys | SSE, default, free |
|
| AWS Managed Keys | aws/service-name, free | 1Y |
| Customer managed Keys | create, 1$/month | 1Y, if enable |
| Customer managed Keys | import, 1$/month | manual, alias |
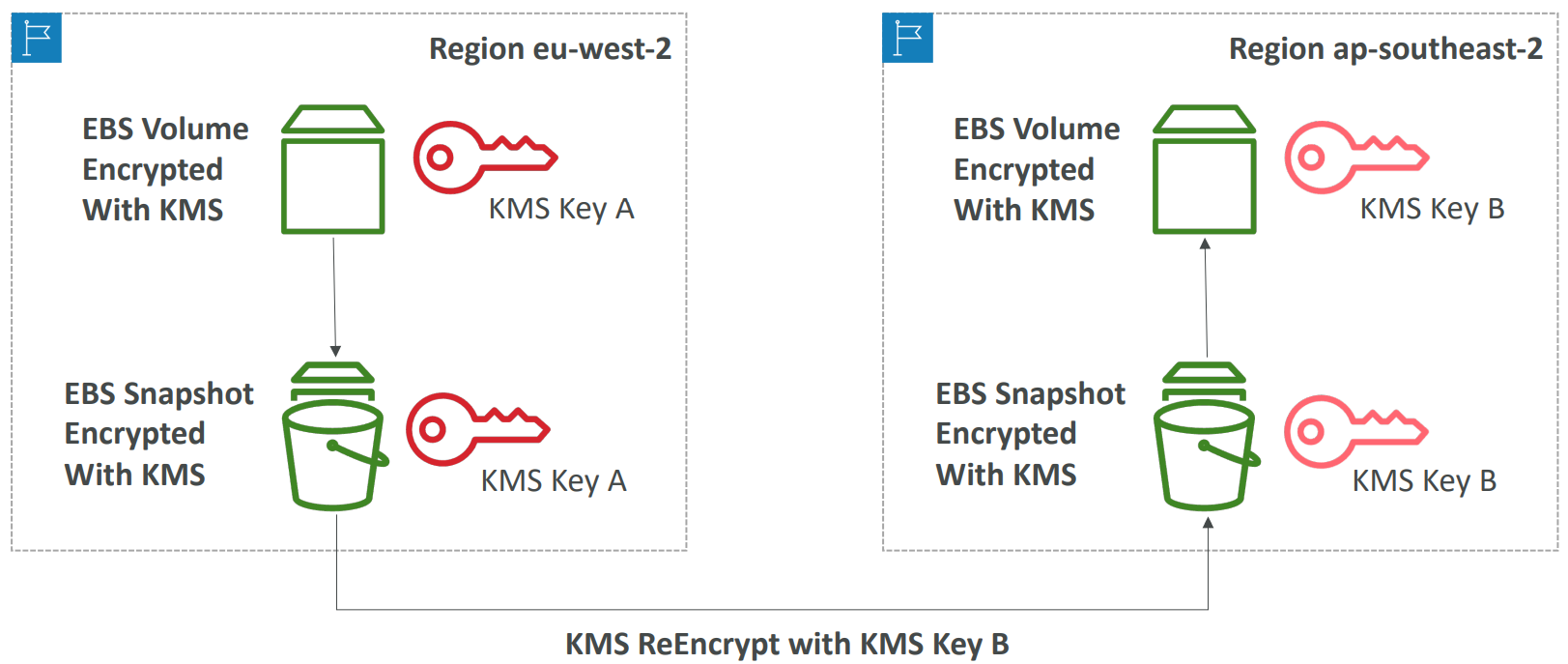
Copying Snapshots across regions
- KMS keys are scoped per region
- diff regions, diff keys
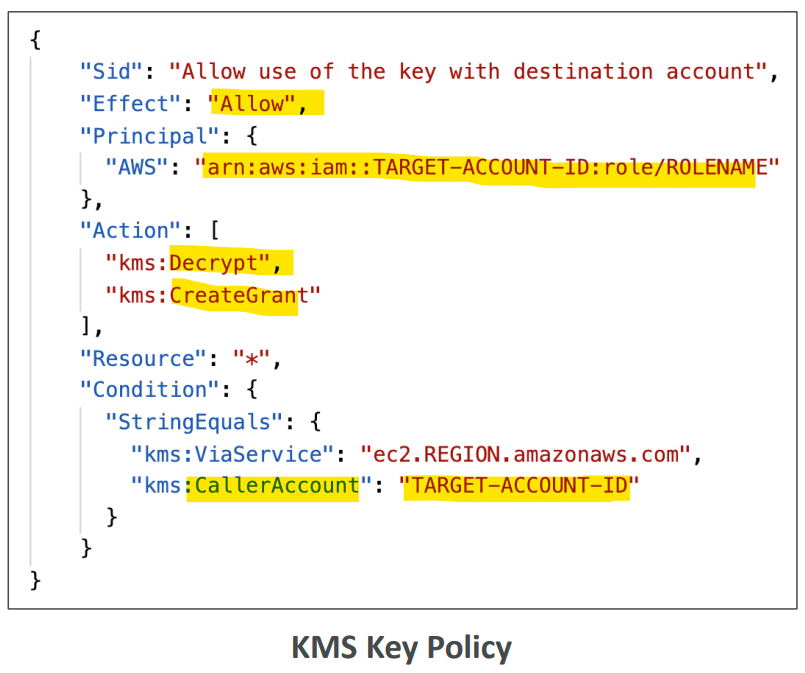
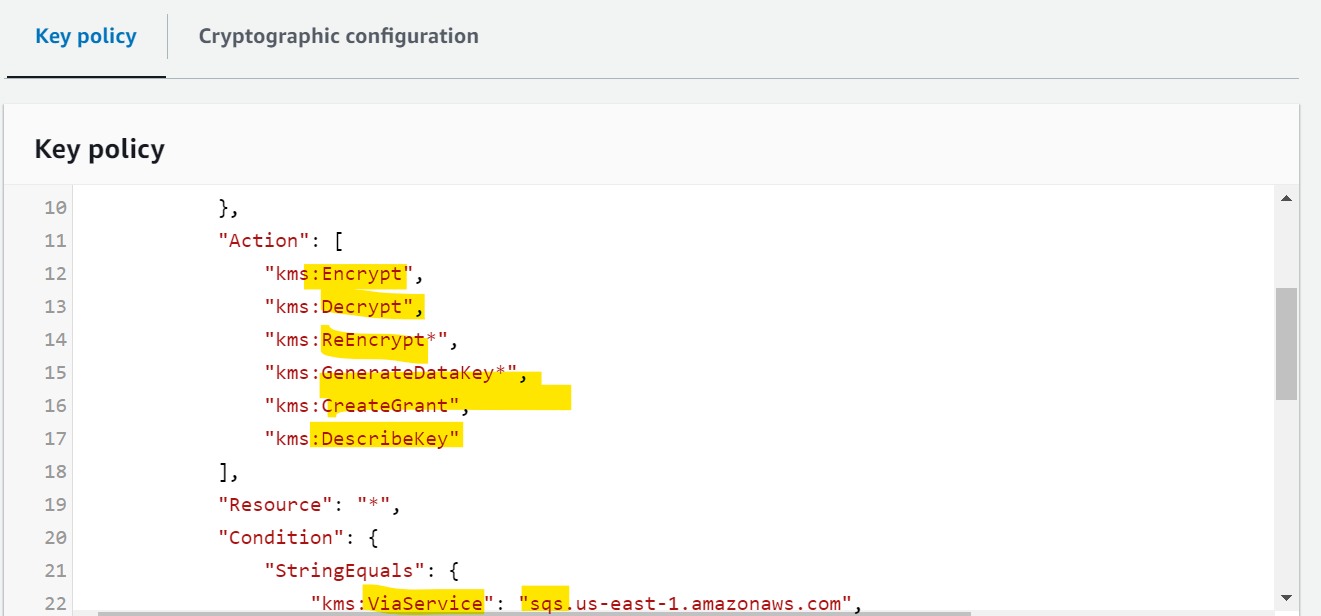
Key Policies
- Control access to KMS keys, “similar” to S3 bucket policies
-
Difference:
- you cannot control access without them(if you don’t define key policy, no one can access it.)
-
Default KMS Key Policy:
- Created if you don’t provide a specific KMS Key Policy
- Complete access to the key to
root user= entire AWS account (every users)
-
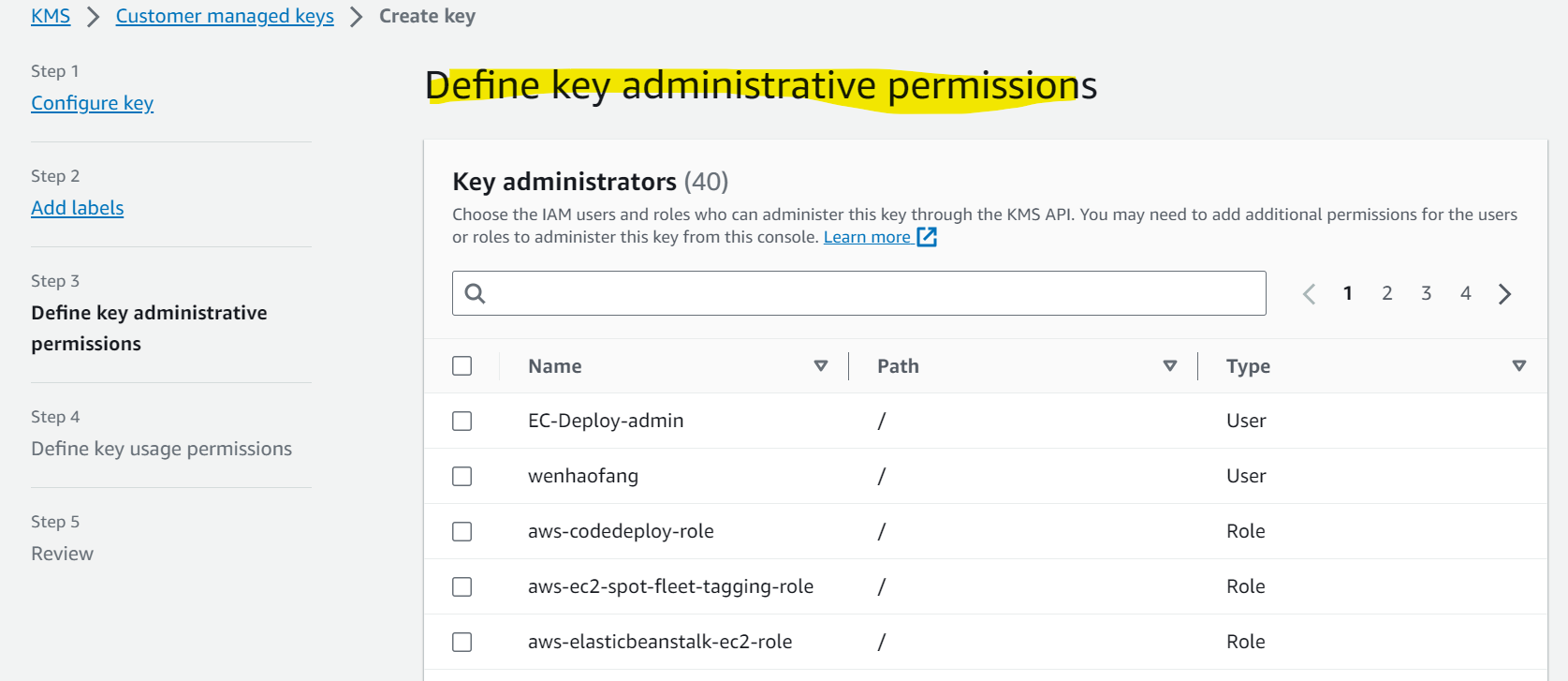
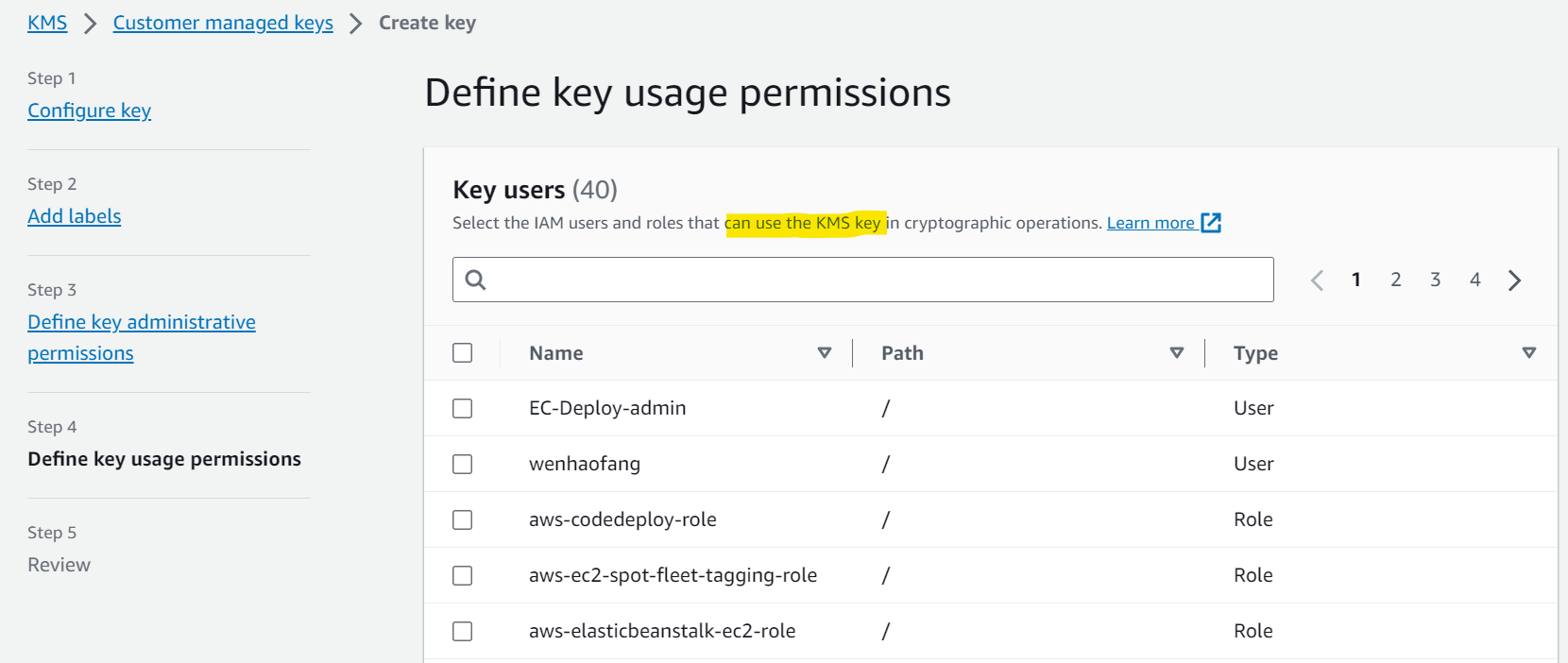
Custom KMS Key Policy:
- Define
users,rolesthat can access the KMS key - Define who can administer the key
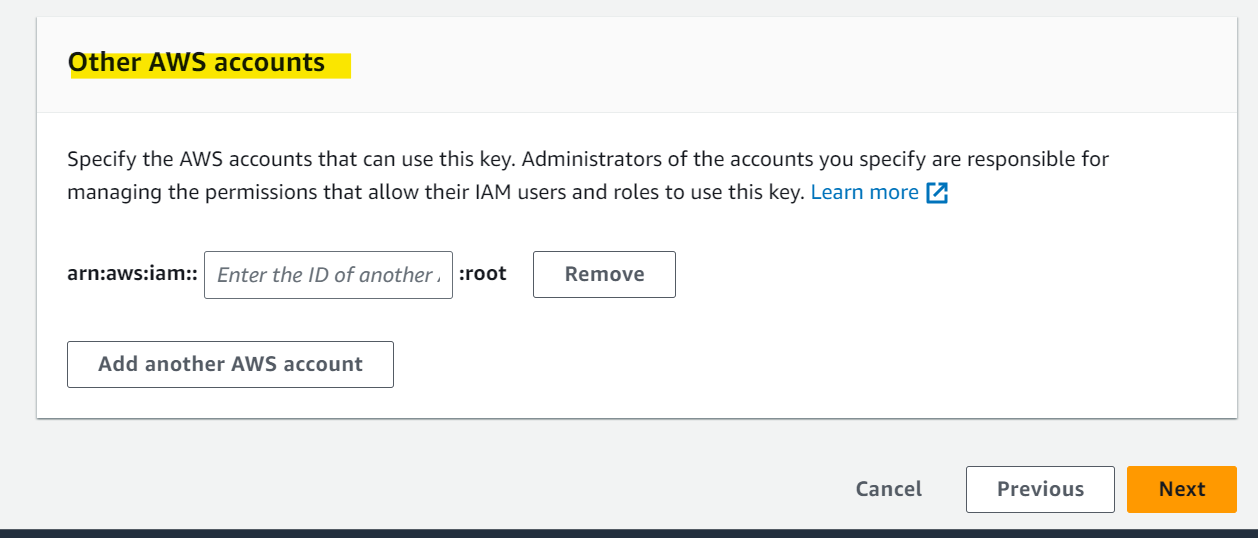
- Useful for cross-account access of your KMS key
- Define
- Sample:
- What should you use to control access to your KMS CMKs?
- KMS Key Policies
- What should you use to control access to your KMS CMKs?
Copying Snapshots across accounts
- Create a Snapshot, encrypted with your own KMS Key (Customer Managed Key)
- Attach a KMS Key Policy to authorize cross-account access
- Share the encrypted snapshot with target account.
- (in target account) Create a copy of the Snapshot, encrypt it with a
CMKin your account - Create a volume from the snapshot
Multi-Region Keys
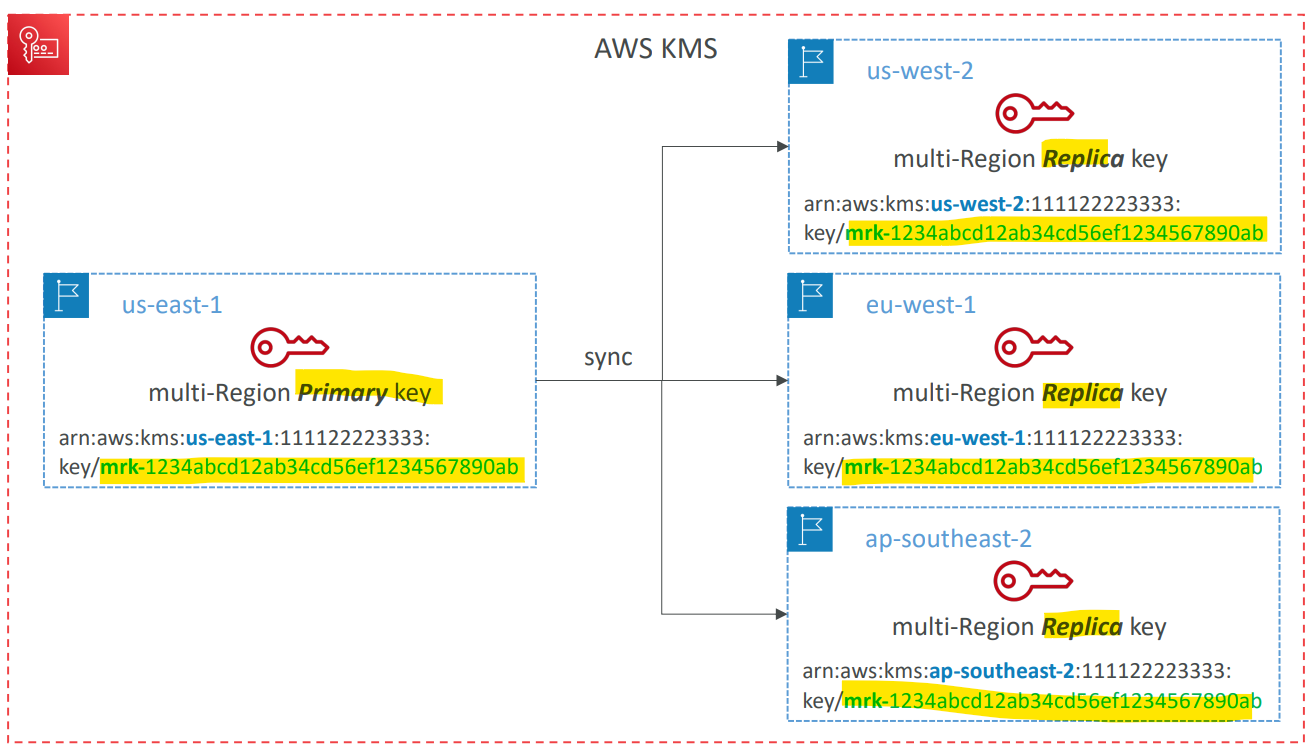
-
Identical KMS keys in different AWS Regions that can be used interchangeably
- allow to Encrypt in one Region and decrypt in other Regions
- No need to re-encrypt or making cross-Region API calls
- Multi-Region keys have the same key ID, key material, automatic rotation…
- KMS Multi-Region are NOT global (Primary + Replicas)
- Each Multi-Region key is managed independently
- Use cases:
- global client-side encryption(have client-side encryption in one region, then have client-side decryption in another region)
- encryption on Global DynamoDB, Global Aurora
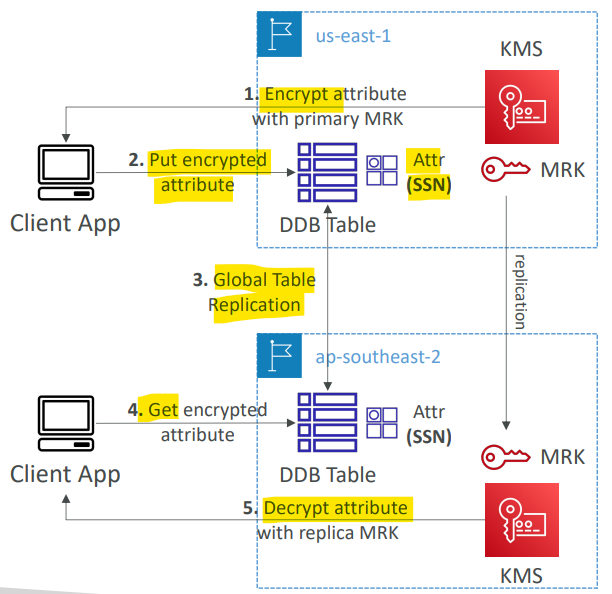
DynamoDB Global Tables and KMS MultiRegion Keys Client-Side encryption
-
DynamoDB Encryption Client- used to encrypt specific attributes client-side in our DynamoDB table
- Combined with
Global Tables, the client-side encrypted data is replicated to other regions
- If we use a
multi-region key, replicated in the same region as the DynamoDB Global table, then clients in these regions can use lowlatency API calls to KMS in their region to decrypt the data client-side - Using
client-side encryptionwe can protect specific fields and guarantee only decryption if the client has access to an API key - Global table 保证跨区数据同步
- multi-region key 保证密钥跨区同步
- client-silde 实现数据在客户端能加解密, 防止传讯过程泄密.
Global Aurora and KMS Multi-Region Keys Client-Side encryption
-
AWS Encryption SDK- used to encrypt specific attributes client-side in our
Auroratable - Combined with
Aurora Global Tables, the client-side encrypted data is replicated to other regions
- used to encrypt specific attributes client-side in our
- If we use a
multi-region key, replicated in the same region as the Global Aurora DB, then clients in these regions can use low-latency API calls to KMS in their region to decrypt the data client-side - Using
client-side encryptionwe can protect specific fields and guarantee only decryption if the client has access to an API key, we can protect specific fields even from database admins
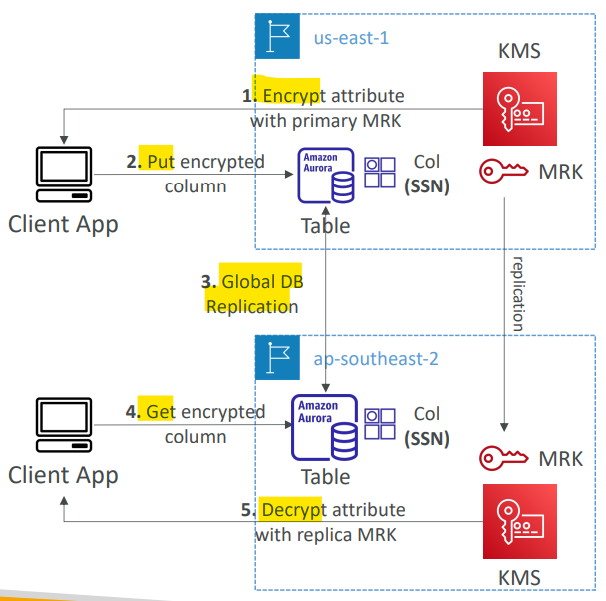
- Sample:
- An online-payment company is using AWS to host its infrastructure. The frontend is created using VueJS and is hosted on an S3 bucket and the backend is developed using PHP and is hosted on EC2 instances in an Auto Scaling Group. As their customers are worldwide, they use both CloudFront and Aurora Global database to implement multi-region deployments to provide the lowest latency and provide availability, and resiliency. A new feature required which gives customers the ability to store data encrypted on the database and this data must not be disclosed even by the company admins. The data should be encrypted on the client side and stored in an encrypted format. What do you recommend to implement this?
- Using Aurora Client-side Encryption and KMS Multi-region Keys.
- An online-payment company is using AWS to host its infrastructure. The frontend is created using VueJS and is hosted on an S3 bucket and the backend is developed using PHP and is hosted on EC2 instances in an Auto Scaling Group. As their customers are worldwide, they use both CloudFront and Aurora Global database to implement multi-region deployments to provide the lowest latency and provide availability, and resiliency. A new feature required which gives customers the ability to store data encrypted on the database and this data must not be disclosed even by the company admins. The data should be encrypted on the client side and stored in an encrypted format. What do you recommend to implement this?
S3 Replication Encryption Considerations
-
SSE-S3- Unencrypted objects and objects encrypted with
SSE-S3are replicated by default
- Unencrypted objects and objects encrypted with
-
SSE-C- Objects encrypted with
SSE-C (customer provided key)are never replicated
- Objects encrypted with
-
SSE-KMS-
For objects encrypted with
SSE-KMS, you need to enable the option- Specify which
KMS Keyto encrypt the objects within the target bucket - Adapt the
KMS Key Policyfor the target key - An
IAM Rolewithkms:Decryptfor the sourceKMS Keyandkms:Encryptfor the targetKMS Key - You might get KMS throttling errors, in which case you can ask for a
Service Quotasincrease
- Specify which
-
-
multi-region AWS KMS Keys- You can use
multi-region AWS KMS Keys, but they are currently treated as independent keys by AmazonS3. 可以用 multi, 但实际上视作独立- the object will still be decrypted and then encrypted
- You can use
-
Sample:
- You have an S3 bucket that is encrypted with
SSE-KMS. You have been tasked to replicate the objects to a target bucket in the same AWS region but with a different KMS Key. You have configured the S3 replication, the target bucket, and the target KMS key and it is still not working. What is missing to make the S3 replication work?- have to configure permission for both Source KMS key
kms:Decryptand Target KMS Keykms:Encryptto be used by S3 Replication service.
- have to configure permission for both Source KMS key
- You have an S3 bucket that is encrypted with
AMI Sharing Process Encrypted via KMS
AMIin Source Account is encrypted withKMS Keyfrom Source Account- Must modify the image attribute to add a Launch Permission which corresponds to the specified target AWS account
- Must share the
KMS Keysused to encrypted the snapshot the AMI references with the target account / IAM Role - The IAM Role/User in the target account must have the permissions to
DescribeKey,ReEncrypted,CreateGrant,Decrypt - When launching an EC2 instance from the AMI, optionally the target account can specify a new
KMS keyin its own account to re-encrypt the volumes
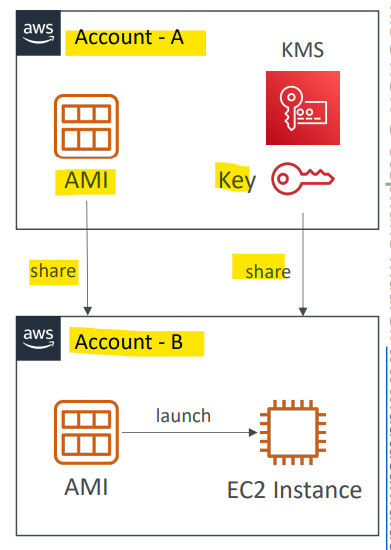
- Sample:
- You have an AMI that has an encrypted EBS snapshot using
KMS CMK. You want to share this AMI with another AWS account. You have shared the AMI with the desired AWS account, but the other AWS account still can’t use it. How would you solve this problem?- need to share KMS CMK with other account
- You have an AMI that has an encrypted EBS snapshot using
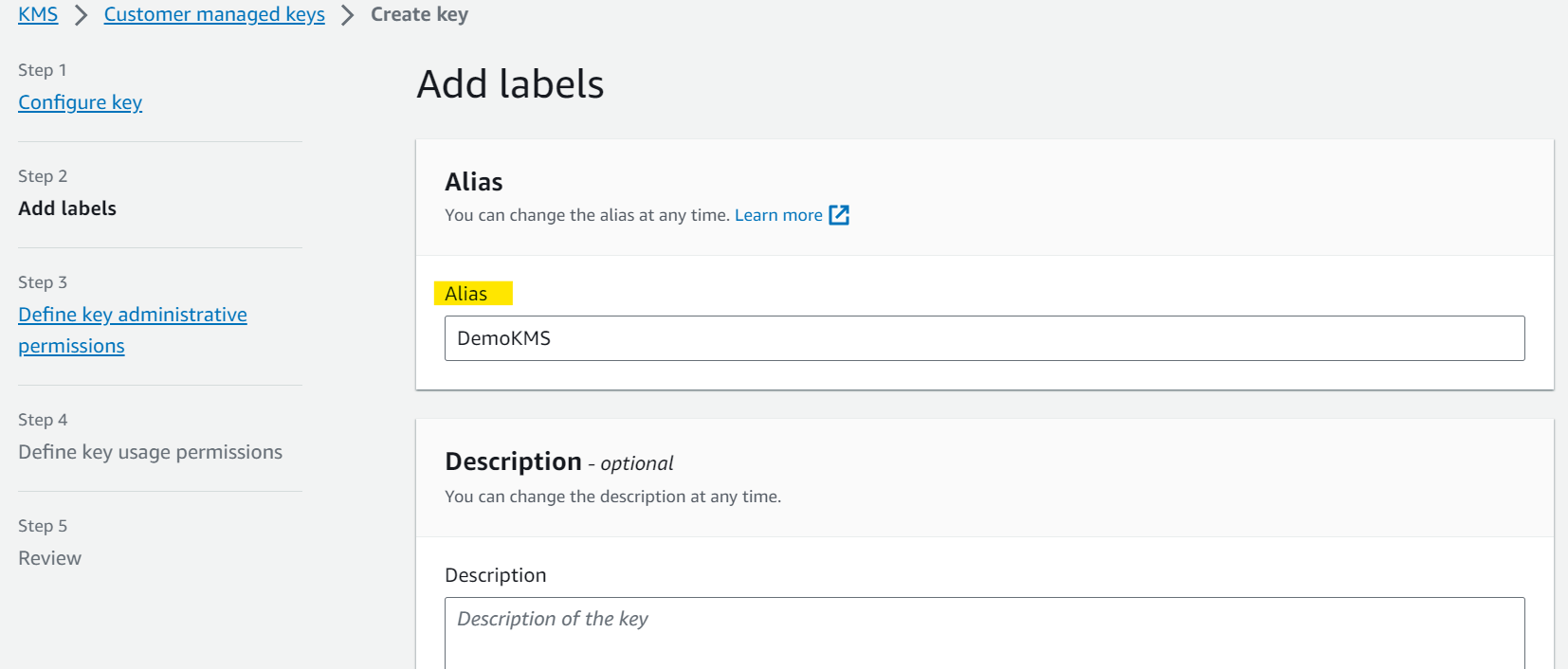
Hands-on
- AWS managed keys
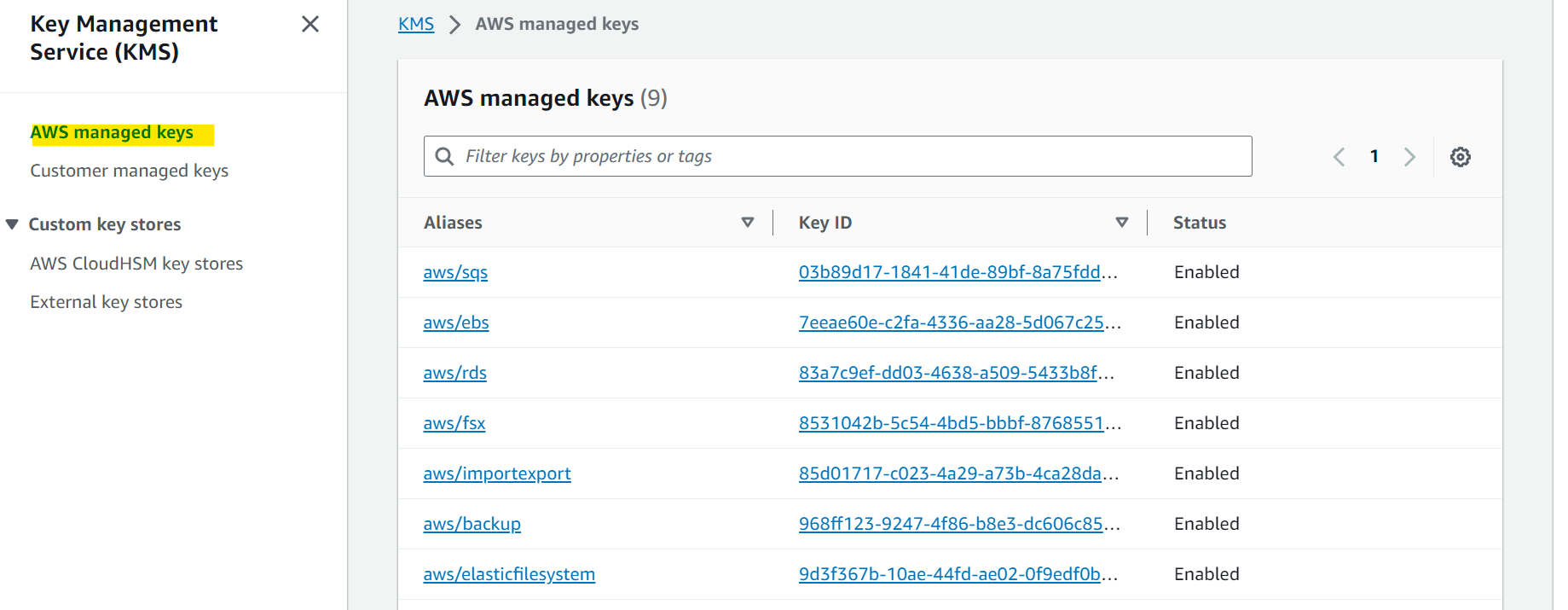
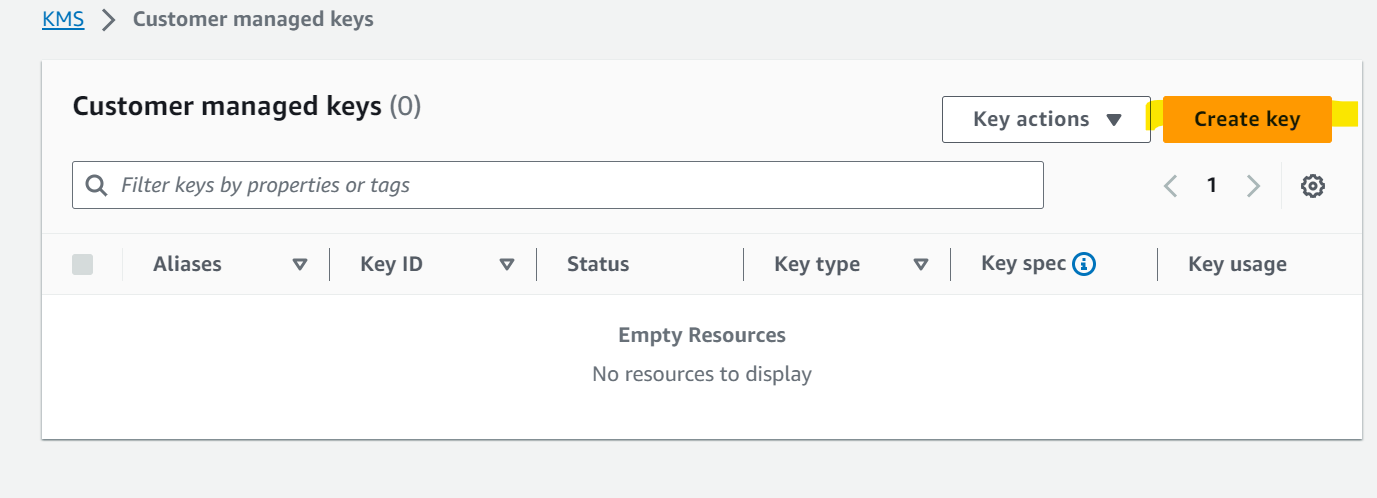
- Customer managed keys
- Rotation
- must enable
- every year